According to Symantec researchers, the Clipminer botnet has already brought its operators at least $1.7 million by intercepting other people’s transactions and mining cryptocurrencies on infected machines.
The researchers say that Clipminer is based on the source code of another trojan, KryptoCibule, which means that it can be either a copycat or a more advanced version of the latter. Clipminer was noticed in January 2021, shortly after KryptoCibule was described in detail by ESET experts, which is another argument in favor of the “rebranding” of the malware.
Let me remind you that we also wrote that New Windows Trojan steals passwords from Chrome and stores them in MongoDB database.
In total, Symantec researchers identified 4375 unique cryptocurrency wallet addresses to which the funds stolen by Clipminer were transferred. Experts found approximately 34.3 BTC and 129.9 ETH in wallets controlled by attackers, and it is believed that other funds were previously withdrawn and “laundered” using mixer services.
The DLL creates a new registry entry and places itself in the C:\Windows\Temp\ folder under a random name. Its purpose is to profile the infected host and download and install the Clipminer payload via Tor.
The malware itself launches the Onion service v3 with a unique address, monitors all keyboard and mouse actions on the infected computer, and also checks running processes to identify any analytical tools.
When there is no activity on the host, i.e. the user is not present, Clipminer starts the XMRig miner for Monero mining, configured to use all available CPU power. Since monitoring of the machine is absent, there is no risk that someone will notice the slowdown in system performance.
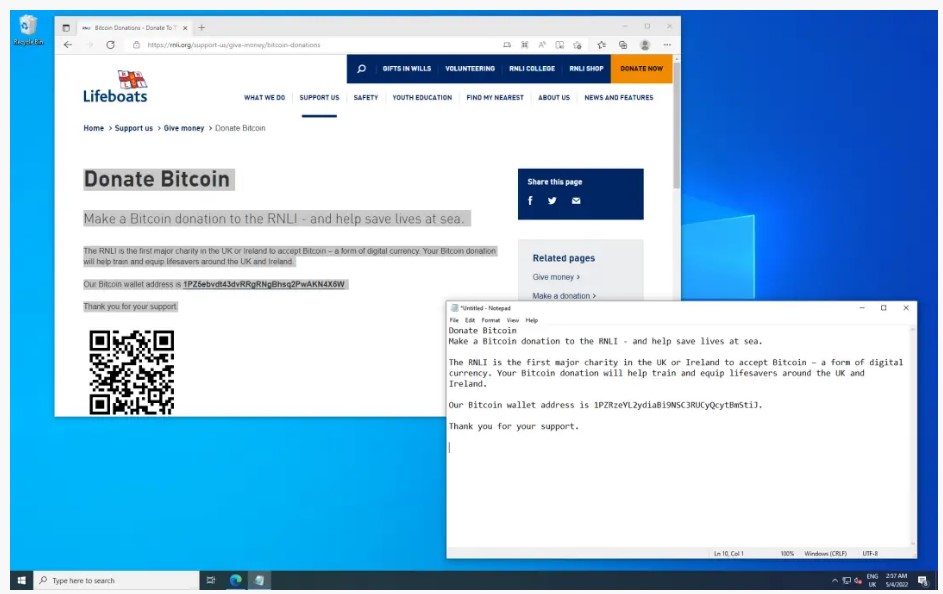
Clipminer changed wallet address
At the same time, the malware constantly controls the clipboard in search of copied cryptocurrency addresses and immediately replaces them with addresses belonging to the attackers, thus stealing other people’s payments.

Leave a Comment