Over 360 million records leaked from Super VPN after a Chinese developer left the app’s database insecure and accessible from the internet.
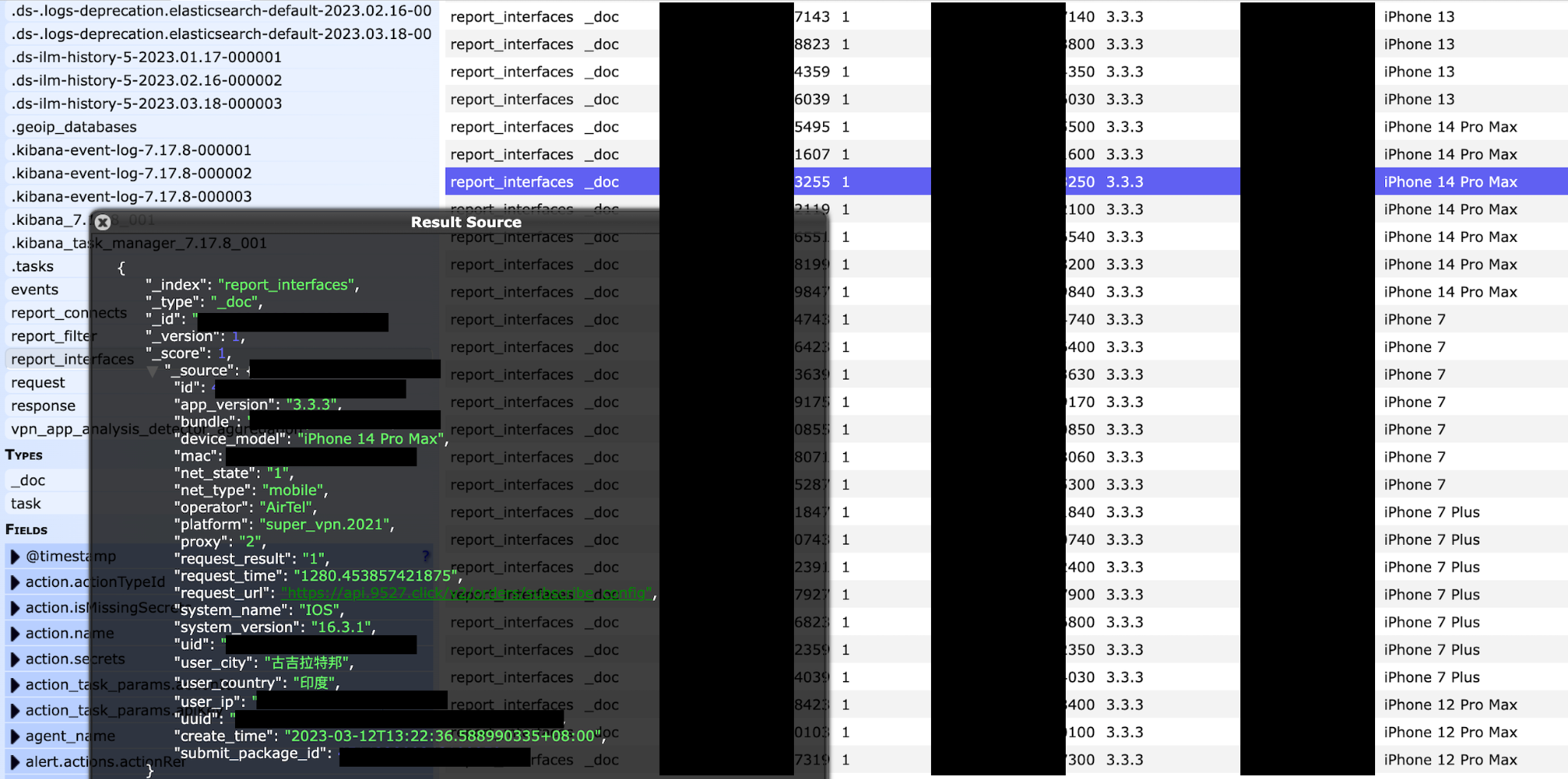
The database contained information about all paid clients of the service, including email addresses, real IP addresses, information about geolocation and VPN servers to which users connected.
Let me remind you that we also wrote that Android Traffic Leaks Outside VPN Tunnels even with Always-on VPN Enabled, and also that NordVPN and TorGuard talk about compromise.
And the media wrote that Russia Blocks Popular VPN Services Such as Proton VPN.
The Super VPN leak was discovered by cybersecurity specialist Jeremiah Fowler. He writes that this is very disturbing news, since Super VPN has more than 100 million downloads worldwide in the Google and Apple app stores.
At the same time, the description of the application in the App Store states that the service does not store any logs, although the permissions of the application allow it to access files, images and other information on the device.
After reviewing a limited sample of records, the researcher reported the issue to all available email addresses associated with Super VPN apps. As a result, the database was secured, but the researcher never received any responses or comments from the developers.
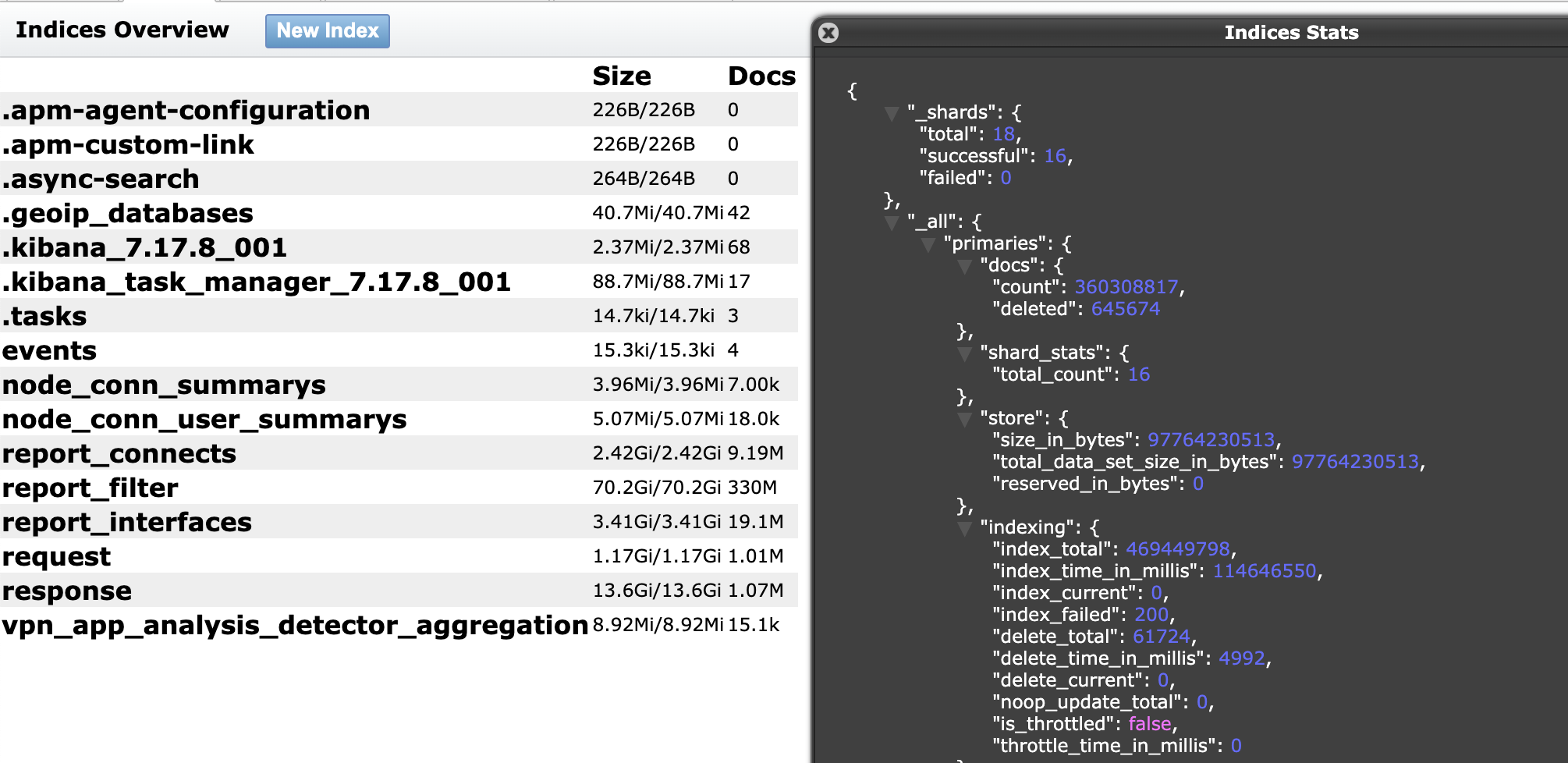
Fowler says that in total the leak consisted of 360,308,817 records and “weighed” 133 GB. In addition to the data already listed above, the records in the database contained secret keys, unique user identifiers, and UUID numbers. Also found in the database:
- additional information, including phone or device model, operating system, internet connection type, and app version;
- refund requests;
- and even links to sites visited by Super VPN users, which allowed them to trace their activities and posed a direct threat to privacy.
Moreover, support emails have also been associated with services such as Storm VPN, Luna VPN, Radar VPN, Rocket VPN and Ghost VPN (not to be confused with CyberGhost VPN). And references to the names of these VPN services were found in the database. Fowler writes that he’s not sure if these VPNs are from the same company, but suggests they’re connected in some way.

Zak Doffman
The expert also noted that back in 2020, information security journalist Zak Doffman warned that Chinese developers had repeatedly tried, but failed to eliminate some critical vulnerability in the application that exposed users to the risk of man-in-the-middle attacks.

Leave a Comment