This article intends to help you delete Lltt Ransomware for free. Our manual also explain how any .lltt files can be restored.
Lltt Virus
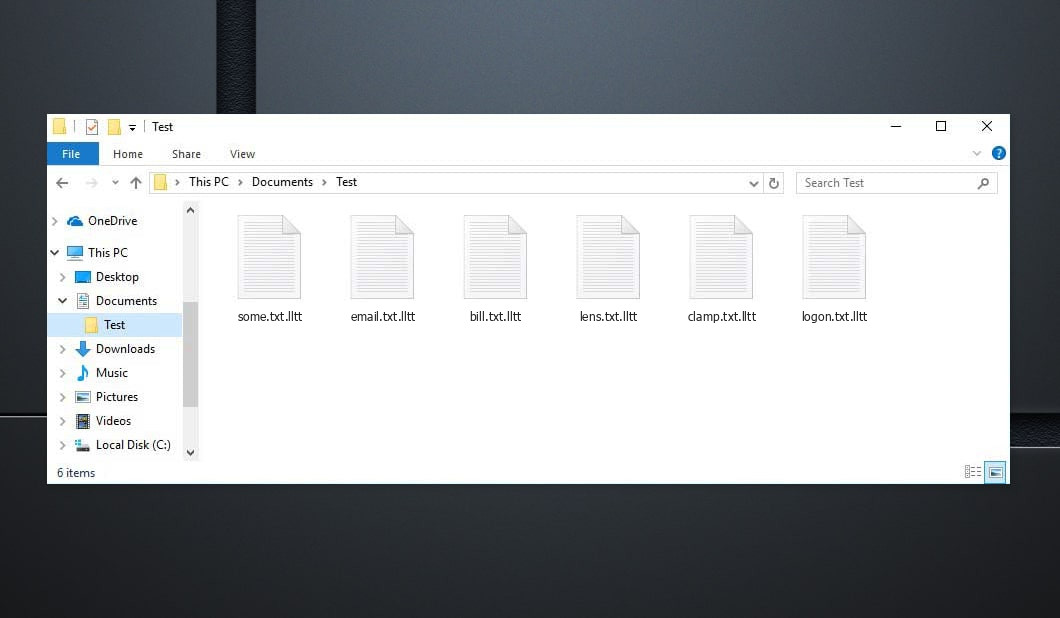
The Lltt Ransomware means a COMPUTER danger utilized to blackmail its sufferers. Lltt Virus might not point to any obvious signs and symptoms, yet its visibility is only uncovered as quickly as its job is executed.
The absence of symptoms is among the main difficulties with this sort of PC viruses. They can permeate into the struck system unnoticed, and also execute their job without revealing their activity in the workstation. This is why most customers are not able to do anything to terminate the virus prior to it has actually completed its objective, and also the goal of this one, in particular, is to make its targets' documents unusable using data ciphering and afterwards suggesting a ransom demand.
The customer is reported by means of a message that this infection puts on their screen that their only solution of bringing their data back is through the repayment of a particular quantity of funds. This blackmailing part of this rip-off is incredibly popular amongst the scams, as well as there's an entire group of PC malware that's utilized in this manner. This malware group is called Ransomware, and also the malware we are currently focusing on certainly falls under it.
The Lltt malware is only disclosed once it has completed encrypting the files. The .lltt Ransomware will after that reveal its demands through an daunting pop-up alert.It is by means of this alert that the customers learn how they are anticipated to transfer their funds to the cyber fraudulences in charge of the Ransomware infection. In many instances, the ransom money would certainly be asked in a cryptocurrency - BitCoin. These cryptocurrencies are really hard to trace, and a typical customer would certainly have no chance of recognizing who they are really moving their funds to. This, as a matter of fact, makes it truly not likely that the hacker's true identity would ever obtain disclosed. It is fairly uncommon for a Ransomware cyberpunk to stand on trial, and the application of cryptocurrency as the suggested payment service is the major reason for that.
Listed below you can find the quote from the Lltt text file:
ATTENTION! Don't worry, you can return all your files! All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: https://we.tl/t-2P5WrE5b9f Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that's price for you is $490. Please note that you'll never restore your data without payment. Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours. To get this software you need write on our e-mail: restorealldata@firemail.cc Reserve e-mail address to contact us: gorentos@bitmessage.ch Our Telegram account: @datarestore
How to Lltt virus encrypt your files?
The .lltt Virus document security is not mosting likely to be eliminated after the ransomware is removed. The .lltt Virus document encryption access key is promised to be given to you when you pay the ransom amount.
However, it is not uncommon for the criminals who support such risks to assure their victims a decryption trick for their encrypted records only to reject to provide that essential as quickly as the payment gets refined. Needless to mention, if you wind up in a problem such as this, you would not be capable of doing anything about it-- your funds would be gone, and your information would still be unattainable. This is why it isn't really sensible idea to transfer the payment, in addition, if you have not gone with any type of alternate choices that may work.
Although we discussed that the security would certainly continue to be on your files even after the Ransomware is no longer in the system, erasing the virus is still extremely vital. After you get rid of the Ransomware, you may likewise try the different data recovery options we have actually created for you, and additionally your new files will not go to threat of being encrypted. To erase this cryptoviral danger, you are recommended to finish the steps you will certainly run into listed below.
Lltt SUMMARY:
| Name | .lltt Virus |
| Type | Ransomware |
| Threat Level | High (Ransomware is thus far the most awful malware you can experience) |
| Symptoms | A Ransomware threat similar to this one would generally not reveal its existence till the papers obtain locked up |
| Promotion Channel | Channels like spam e-mail promotion, and malvertising are normally the ones used to spread Ransomware. |
| Data Recovery Solution | Emsisoft Decrypter |
| Detection Utility |
.lltt may recover itself plenty of times if you don't get rid of its core files. We suggest downloading Loaris Trojan Remover to scan for malicious utilities. This may save you a lot of time and efforts to effectively get rid of all possible malware within your device.
Read more about Loaris Trojan Remover (License Agreement, Privacy Policy ).
If Loaris identifies a threat, you will need to buy a license to get rid of it. |
Delete Lltt Virus Ransomware
Some of the steps will likely demand you to exit the page. Bookmark it to easily get back to it later.
Reboot in Safe Mode (use this tutorial if you don’t know how to do it).
Click CTRL + SHIFT + ESC simultaneously and go to the Processes Tab. Try to identify which processes are malicious.
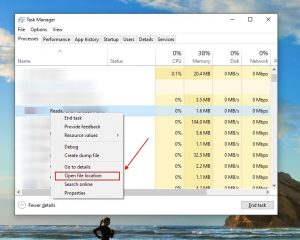
Right click on each of them and choose Open File Location. Then inspect the documents with online file checker:
Once you open their folder, end the processes that are contaminated, then get rid of their folders.
Note:If you are particular something is part of the threat - eliminate it, even if the scanner does not note it. No anti-virus application can recognize all infections.
Keep holding the Win + R. And then copy & paste the following:
- notepad %windir%/system32/Drivers/etc/hosts
A new document will certainly open. In case you are hacked, there will be a load of other IPs connected to your device near the bottom. Examine the image below:
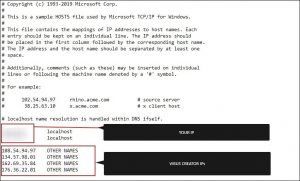
In case there are suspicious IPs below “localhost” – get in touch with us in the comments.
Use CTRL + SHIFT + ESC simultaneously and access the Startup Tab:
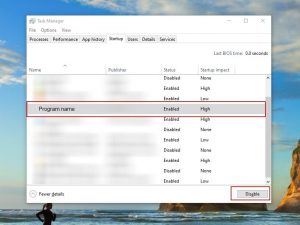
Proceed to Program Name and select “Disable”.
Keep in mind that ransomware may even include a fake developer name to its process. You must check out every process and be persuaded that it is legitimate.
To get rid of Lltt Virus, you may have to deal with system files and registries. Making a mistake and getting rid of the wrong thing may hurt your device.
You can prevent the system damage by selecting Loaris Trojan Remover - a high-quality Lltt removal software.
Read review about Loaris Trojan Remover (License Agreement, Privacy Policy ).
Look for the ransomware in your registries and get rid of the entries. Be very careful – you can destroy your system if you remove entries not associated with the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Get rid of everything in Temp. Finally, simply check out for anything lately added. Don't forget to drop us a comment if you run into any issue!
How to Decrypt .lltt files?
Djvu Ransomware essentially has two versions.
- Old Version: Most older extensions (from “.djvu” up to “.carote”) decryption for most of these versions was previously supported by STOPDecrypter tool in case if infected files with an offline key. That same support has been incorporated into the new Emsisoft Decryptor for these old Djvu variants. The decrypter will only decode your files without submitting file pairs if you have an OFFLINE KEY.
- New Version: The newest extensions released around the end of August 2019 after the ransomware was changed. This includes .coharos, .shariz, .gero, .hese, .xoza, .seto, peta, .moka, .meds, .kvag, .domm, .karl, .nesa, .boot and etc….These new versions were supported only with Emsisoft Decryptor.
"The decrypter can't decrypt my files?"
In most cases this means you have an online ID. It could likewise suggest your data were secured by a newer variant of STOP/Djvu.
- Offline ID. When the ransomware can not connect to its command as well as control web servers while encrypting your data, it uses an integrated file encryption key and also an integrated ID. Offline ID's generally finish in t1 and also are normally easy to recognize. Since the offline key and ID just transform with each variant/extension, every person who has had their files encrypted by the very same version will certainly have the same ID and also the data will be decryptable by the exact same key (or "exclusive key in the case of RSA file encryption).
- Online ID. For the most part the ransomware has the ability to connect to its command as well as control web servers when it secures files, and also when this happens the servers respond by producing arbitrary keys for each contaminated computer. Given that each computer has its own key, you can't use a key from an additional computer to decrypt your data. The decrypter can functioning about this with older variants as long as it has some help, nevertheless for more recent versions there is absolutely nothing that can be done to recover files.
In case when the tutorial doesn’t help, download the anti-malware tool we suggest or try free online virus checker. Furthermore, you may always ask us in the comments for assistance!

Leave a Comment