Earlier this month, analysts from Cluster25 discovered a new Erbium infostealer and, as their colleagues from Cyfirma now report, the malware is distributed under the guise of cracks and cheats for popular games and steals credentials and information about cryptocurrency wallets from victims.
Let me remind you that we also talked about the fact that Prynt Stealer Malware Contains a Backdoor and Steals Data from Hackers, and also that Unusual YTStealer Malware Targets YouTubers.
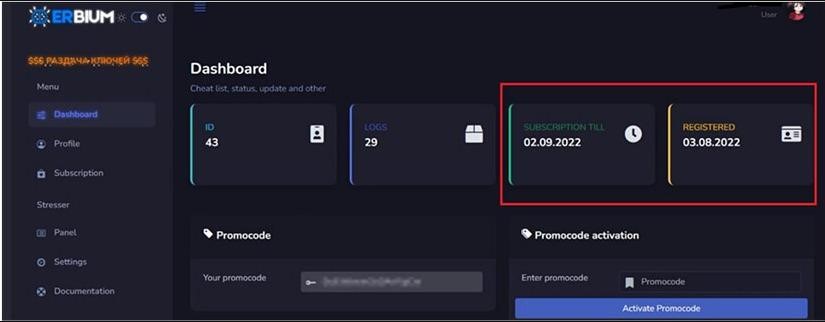
Erbium is a new MaaS (Malware-as-a-Service) focused on information theft. According to experts, the malware is already gaining popularity in the hacker community due to its very extensive functionality, customer support and competitive prices.
Erbium has been advertised mainly on Russian-speaking hack forums since July 2022, and there is still very little information about its actual use by attackers. At the start, the malware cost only $9 per week, but as its popularity grew, the price increased, and by the end of August it was already $100 per month, or $1,000 for an annual license. Thus, now Erbium is about a third cheaper than the popular RedLine infostealer.
Like other data-stealing malware, Erbium is able to steal information stored in victims’ browsers (based on Chromium or Gecko), including passwords, cookies, bank card data and autofill. The malware is also capable of extracting data about various cryptocurrency wallets installed in browsers as extensions.
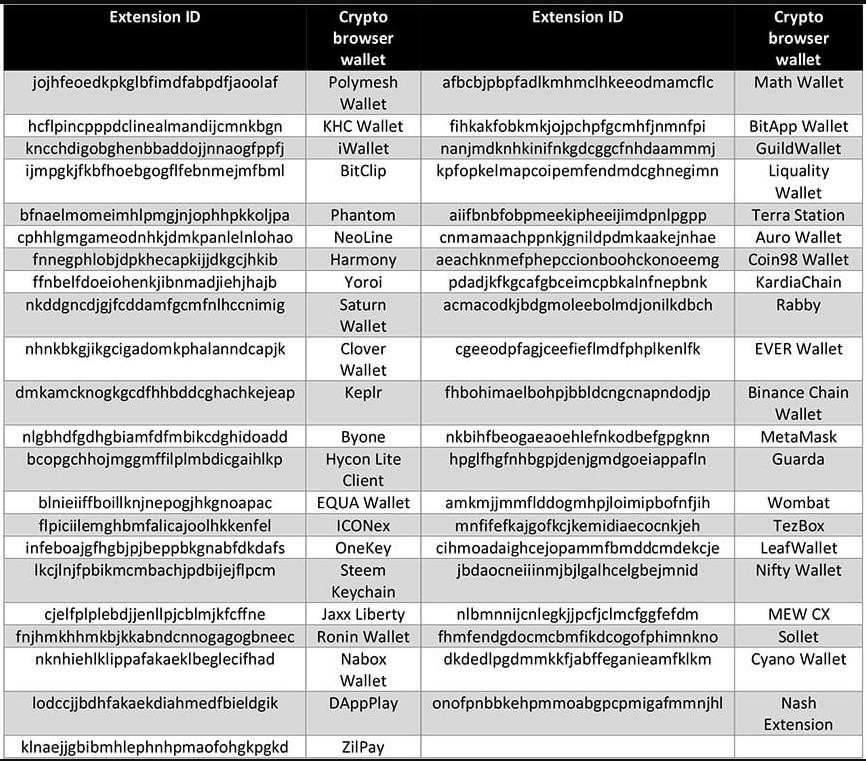
In addition, the infostealer is “interested” in cold dektop wallets, including Exodus, Atomic, Armory, Bitecoin-Core, Bytecoin, Dash-Core, Electrum, Electron, Coinomi, Ethereum, Litecoin-Core, Monero-Core, Zcash and Jaxx.
Can Erbium and steal two-factor authentication codes from Trezor Password Manager, EOS Authenticator, Authy 2FA and Authenticator 2FA.
In addition to the above, the malware is able to take screenshots from all monitors of the attacked user, steal tokens from Steam and Discord, steal Telegram authentication files, and can create a profile of the infected host based on the OS and hardware it uses.
All data collected by the infostealer is transmitted to the control server through the built-in API system, and in the admin panel, malware operators see what exactly was stolen from each infected host. The malware uses three URLs to connect to the control panel, including the Discord CDN, which is still actively abused by hackers.
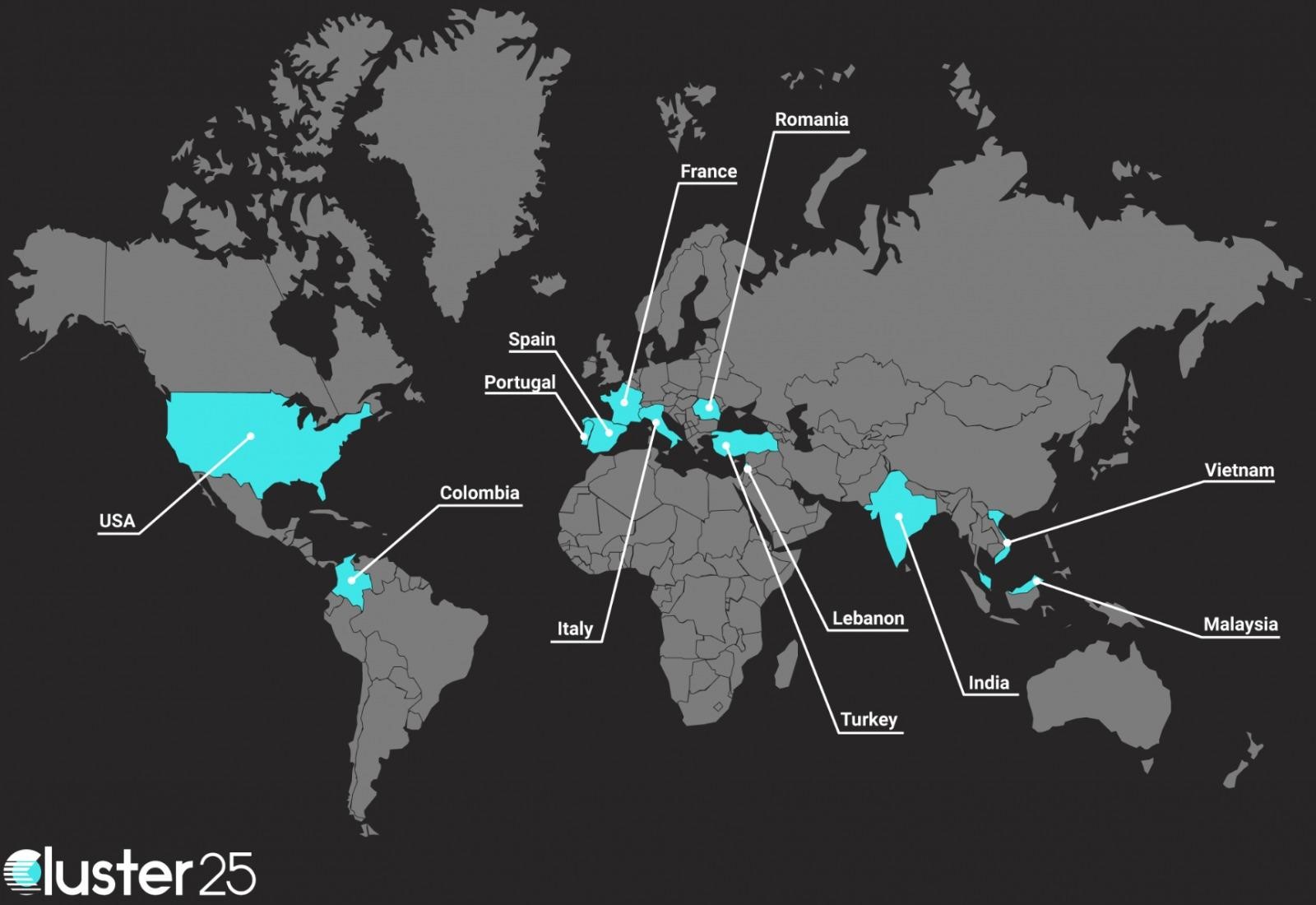
According to Cluster25, signs of Erbium contamination can already be found almost all over the world, including in the US, France, Colombia, Spain, Italy, India, Vietnam and Malaysia.
Although the Erbium distribution campaign uncovered by Cyfirma analysts uses game cracks and cheats as baits, and malware enters victims’ systems through drive-by downloads, experts warn that malware distribution channels may change depending on buyers’ preferences.

Leave a Comment