This article intends to help you delete Alka Ransomware at no cost. 我们的说明还解释了如何 .alka files 可以解密.
About Alka
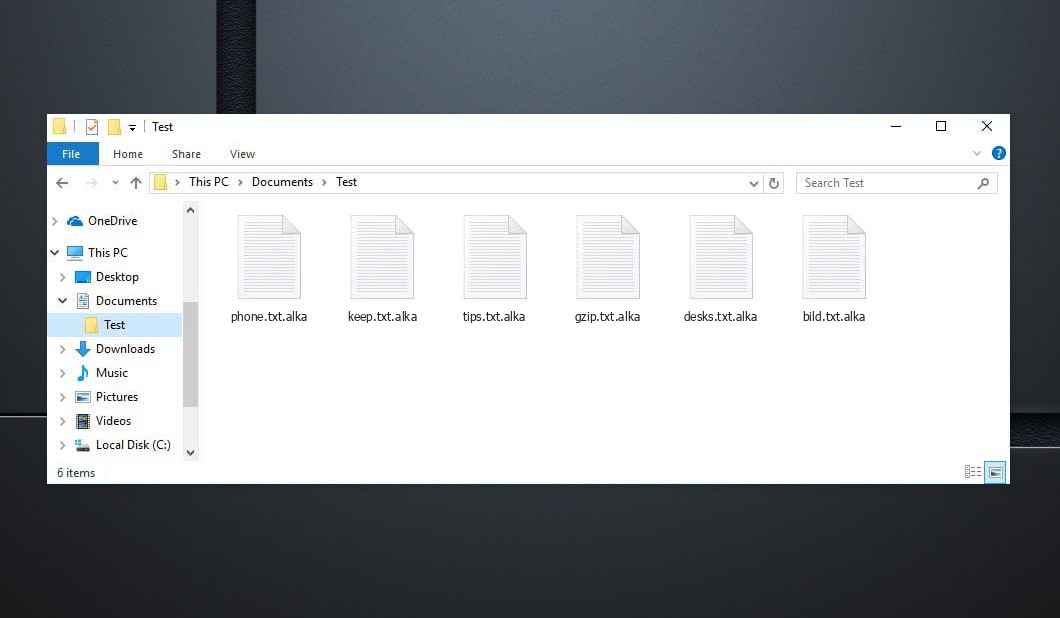
Alka Ransomware represents a cryptovirology PC risk made use of to blackmail its targets. Alka 病毒可能不会指向任何类型的明显迹象, yet its visibility is just uncovered as quickly as its work is performed.
The absence of signs is one of the major difficulties with this type of COMPUTER viruses. They can permeate into the struck system unnoticed, 以及执行他们的工作而不在工作站中显示他们的任务. This is why most clients are unable to do anything to terminate the virus prior to it has actually completed its mission, 以及这个的目标, 尤其, is to make its victims' files pointless through information ciphering and then indicating a ransom demand.
The individual is reported via a message that this infection puts on their screen that their only remedy of bringing their information back is using the settlement of a particular amount of funds. This blackmailing part of this scam is popular among the scams, and there's an entire team of COMPUTER malware that's used in this manner. 该恶意软件类别称为勒索软件, and the malware we are currently focusing on absolutely falls under it.
这 Alka 恶意软件只有在完成对文档的加密后才会被披露. 这 .alka Ransomware will certainly then express its needs through an challenging pop-up alert.It is by means of this alert that the customers find out just how they are anticipated to transfer their funds to the cyber frauds responsible for the Ransomware infection. 在大多数情况下, 赎金肯定会以加密货币形式索取 - 比特币. 这些加密货币确实很难追踪, as well as a common individual would have no chance of knowing that they are actually moving their funds to. 这, 事实上, makes it actually not likely that the hacker's real identification would ever get disclosed. 勒索软件黑客出庭受审的情况相当罕见, as well as the application of cryptocurrency as the recommended payment service is the major reason for that.
Below you can discover the quotation from the Alka text file:
注意力! 不用担心, 您可以归还所有文件! 您的所有文件(如照片), 数据库, 文件和其他重要文件均使用最强的加密和唯一密钥进行加密. 恢复文件的唯一方法是为您购买解密工具和唯一密钥. 该软件将解密您所有的加密文件. 你有什么保证? 您可以从您的电脑发送您的加密文件之一,我们将免费解密它. 但我们只能解密 1 免费归档. 文件不得包含有价值的信息. 您可以获取并查看视频概述解密工具: https://we.tl/t-2P5WrE5b9f 私钥和解密软件的价格是 $980. 折扣 50% 如果您先联系我们,就可以使用 72 小时, 你的价格是 $490. 请注意,如果不付款,您将永远无法恢复您的数据. 查看你的电子邮件 "垃圾邮件" 或者 "垃圾" 文件夹,如果您没有收到超过 6 小时. 要获取此软件,您需要写在我们的电子邮件中: 恢复所有数据@firemail.cc 保留电子邮件地址以便与我们联系: gorentos@bitmessage.ch 我们的电报帐户: @数据恢复
How to Alka virus encrypt your files?
这 .alka Virus file file encryption is not going to be gotten rid of after the ransomware is removed. 这 .alka 承诺在您支付赎金时向您提供病毒文档加密访问密钥.
然而, it is not uncommon for the hackers who guarantee such risks to promise their sufferers a decryption key for their encrypted papers just to refuse to supply that essential as soon as the repayment gets processed. 没必要讨论, 如果你最终遇到这样的问题, you would not be capable of doing anything regarding it-- 你的资金肯定会消失, 以及您的数据肯定仍然无法获取. This is why it isn't actually smart idea to move the settlement, 此外, if you have not opted for any kind of alternate options that may be effective.
Even though we discussed that the encryption would certainly continue to be on your papers also after the Ransomware is no more in the system, 消灭病毒仍然非常重要. 摆脱勒索软件后, you may likewise try the different documents recuperation services we have actually established for you, as well as likewise your brand-new documents will not be at threat of being secured. 消除这种加密病毒风险, 建议您完成下面您肯定会遇到的步骤.
Alka SUMMARY:
| 姓名 | .alka Virus |
| 类型 | 勒索软件 |
| 威胁级别 | 高的 (勒索软件是迄今为止您能遇到的最糟糕的恶意软件) |
| 症状 | A Ransomware threat such as this one would normally not expose its presence up until the files get locked up |
| 推广渠道 | 垃圾邮件促销等渠道, 和恶意广告通常是用来传播勒索软件的. |
| 数据恢复解决方案 | Emsisoft解密器 |
| 检测实用程序 |
.alka 如果您不删除其核心文件,可能会多次自行恢复. 我们建议下载 Loaris Trojan Remover 来扫描恶意实用程序. 这可以节省您大量的时间和精力,以有效地清除设备中所有可能的恶意软件.
|
Delete Alka Virus Ransomware
某些步骤可能会要求您退出该页面. 书签 以便稍后轻松返回.
重新启动 安全模式 (如果您不知道如何操作,请使用本教程).
点击 控制键 + 转移 + ESC键 同时并转到 进程选项卡. 尝试识别哪些进程是恶意的.
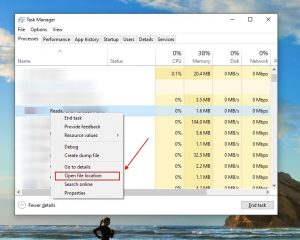
右键点击 对他们每个人进行选择 打开文件所在位置. 然后使用在线文件检查器检查文件:
一旦你打开他们的文件夹, 结束进程 那些被污染的, 然后 删除他们的文件夹.
笔记:如果您确定某物属于危险 - 消除它, 即使扫描仪没有标记它. 没有任何防病毒应用程序可以识别所有感染.
继续按住 赢 + 右. 然后复制 & 粘贴以下内容:
- 记事本%windir%/system32/Drivers/etc/hosts
将打开一个新文件. 万一你被黑了, 底部会有大量链接到您设备的其他 IP. 见下图:
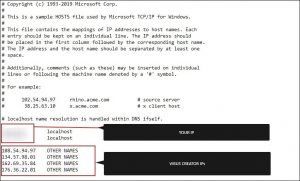
如果下面有可疑的IP“本地主机” – 在评论中与我们联系.
使用 控制键 + 转移 + ESC键 同时并访问 启动选项卡:
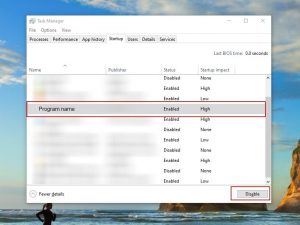
继续 节目名称 并选择“禁用”.
请记住,勒索软件甚至可能在其进程中包含虚假的开发人员名称. 您必须检查每个流程并确信其是合法的.
为了摆脱 Alka Virus, 您可能需要处理系统文件和注册表. 犯错误并摆脱错误的东西可能会损坏您的设备.
您可以通过选择 Loaris Trojan Remover 来防止系统损坏 - A high-quality Alka removal software.
阅读有关的评论 Loaris 木马清除器 (许可协议, 隐私政策 ).
看 为了 勒索软件 在您的注册表中和 摆脱 条目. 要非常小心 - 如果删除与勒索软件无关的条目,您可能会破坏您的系统.
在 Windows 搜索字段中键入以下各项:
- %应用程序数据%
- %本地应用程序数据%
- %程序数据%
- %目录%
- %温度%
摆脱 Temp 中的所有内容. 最后, 只需检查最近添加的任何内容. 如果您遇到任何问题,请不要忘记给我们留言!
How to Decrypt .alka files?
Djvu 勒索软件本质上有两个版本.
- 旧版: 大多数较旧的扩展 (从“.djvu”到“.carote”) 大多数这些版本的解密以前由 STOPDecrypter 工具支持 如果使用离线密钥感染文件. 同样的支持已纳入新的 Emsisoft解密器 对于这些旧的 Djvu 变体. 如果您有文件对,解密器只会解码您的文件而不提交文件对 离线密钥.
- 新版本: 八月底左右发布的最新扩展 2019 勒索软件被更改后. 这包括 .coharos, .沙里兹, .然后, .赫塞, .农场, .濑户, 佩塔, .摩卡, .药物, .嘎嘎, .愚蠢的, .卡尔, .距离, .启动等等....这些新版本仅受 Emsisoft Decryptor 支持.
"解密器无法解密我的文件?"
在大多数情况下,这表明您有一个在线 ID. It could additionally suggest your data were secured by a newer version of STOP/Djvu.
- 离线ID. 当勒索软件在加密文件时无法链接到其命令以及控制 Web 服务器时, it makes use of a built-in file encryption key as well as a built-in ID. 离线 ID 通常结束于 t1 and also are normally simple to identify. 鉴于离线密钥和 ID 仅随每个变体/扩展名进行转换, everybody that has actually had their documents encrypted by the very same variation will have the very same ID as well as the documents will certainly be decryptable by the same key (或者 "RSA文件加密时的独占密钥).
- 在线身份证. Most of the times the ransomware has the ability to link to its command and also control servers when it encrypts files, and also when this happens the servers react by creating random keys for every infected computer system. 考虑到每个计算机系统都有自己的密钥, you can not make use of a key from another computer system to decrypt your files. The decrypter is capable of functioning about this with older versions as long as it has some help, however for more recent variants there is absolutely nothing that can be done to recuperate files.
如果教程没有帮助, 下载我们建议或尝试的反恶意软件工具 免费在线病毒检查器. 此外, 您可以随时在评论中向我们寻求帮助!





i try to decrypt ‘alka’ file with emisoft software but i can’t and there’s explaination like this “error, the remote name could not be resolved”. please help me 🙁