This article intends to help you delete Reqg Ransomware at no cost. 我們的手冊還解釋瞭如何 .reqg files 可以解密.
Reqg Virus
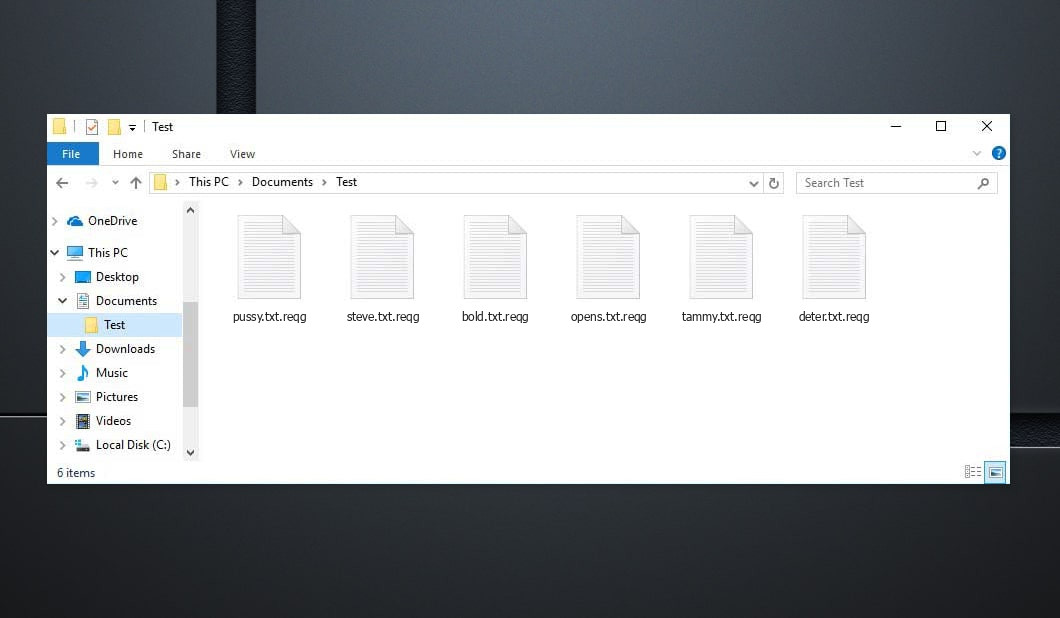
這 Reqg 勒索軟體是一種用來勒索受害者的 PC 威脅. Reqg Infection may not point to any evident signs, 然而它的存在卻在其工作完成後很快就被發現.
The lack of signs is among the major problems with this type of PC infections. 它們可以在不被發現的情況下進入受攻擊的系統, as well as apply their job without revealing their activity in the workstation. This is why most consumers are not able to do anything to end the infection before it has actually finished its objective, 以及這個的目標, 特別, is to make its sufferers' documents pointless through information ciphering and then indicating a ransom demand.
The user is reported using a message that this infection puts on their screen that their only option of bringing their data back is using the settlement of a particular amount of funds. This blackmailing component of this scam is very popular among the fraudulences, and also there's an entire group of PC malware that's used in this way. 該惡意軟件組稱為勒索軟件, 我們目前關注的惡意軟體絕對屬於其中.
這 Reqg 惡意軟件只有在完成文件加密後才會被披露. 這 .reqg Ransomware will certainly then reveal its needs through an challenging pop-up alert.It is via this alert that the individuals discover exactly how they are expected to transfer their funds to the cyber fraudulences responsible for the Ransomware infection. 大多數情況下, 贖金肯定會以加密貨幣形式索取 - 比特幣. 這些加密貨幣確實很難追踪, and also a common customer would certainly have no chance of recognizing who they are really moving their funds to. 這, 實際上, makes it really not likely that the cyberpunk's real identification would certainly ever before obtain revealed. 勒索軟件黑客站在法庭上是相當不尋常的, and the application of cryptocurrency as the suggested settlement service is the primary reason for that.
Below you can find the quote from the Reqg text file:
注意力! 不用擔心, 您可以歸還所有文件! 您的所有文件(如照片), 數據庫, 文件和其他重要文件均使用最強的加密和唯一密鑰進行加密. 恢復文件的唯一方法是為您購買解密工具和唯一密鑰. 該軟件將解密您所有的加密文件. 你有什麼保證? 您可以從您的電腦發送您的加密文件之一,我們將免費解密它. 但我們只能解密 1 免費歸檔. 文件不得包含有價值的信息. 您可以獲取並查看視頻概述解密工具: https://we.tl/t-2P5WrE5b9f 私鑰和解密軟件的價格是 $980. 折扣 50% 如果您先聯繫我們,就可以使用 72 小時, 你的價格是 $490. 請注意,如果不付款,您將永遠無法恢復您的數據. 查看你的郵件 "垃圾郵件" 或者 "垃圾" 文件夾,如果您沒有收到超過 6 小時. 要獲取此軟件,您需要寫在我們的電子郵件中: 恢復所有資料@firemail.cc 保留電子郵件地址以便與我們聯繫: gorentos@bitmessage.ch 我們的電報帳戶: @數據恢復
How to Reqg virus encrypt your files?
這 .reqg Virus document file encryption is not going to be eliminated after the ransomware is removed. 這 .reqg 承諾在您支付贖金時向您提供病毒文檔加密訪問密鑰.
儘管如此, it is not uncommon for the criminals that support such threats to assure their victims a decryption trick for their encrypted documents just to refuse to give that essential as soon as the settlement obtains processed. 沒必要討論, 如果你遇到這樣的情況, 你對此無能為力-- 你的資金肯定會消失, 而且您的數據肯定仍然難以訪問. This is why it isn't really wise thought to transfer the settlement, 此外, if you haven't chosen any different options that may be effective.
Although we pointed out that the security would remain on your documents even after the Ransomware is no longer in the system, 消除感染仍然非常重要. 消除勒索軟件後, you may likewise attempt the alternative file recovery services we have actually developed for you, as well as also your brand-new data won't go to threat of being secured. 為了消除這種加密病毒威脅, you are advised to finish the actions you will certainly run into below.
Reqg SUMMARY:
| 姓名 | .reqg Virus |
| 類型 | 勒索軟件 |
| 威脅級別 | 高的 (勒索軟件是迄今為止您遇到過的最可怕的惡意軟件) |
| 症狀 | A Ransomware threat such as this one would normally not disclose its visibility up until the files obtain secured |
| 推廣渠道 | 垃圾郵件促銷等渠道, 和惡意廣告通常是用來傳播勒索軟件的. |
| 數據恢復解決方案 | Emsisoft解密器 |
| 檢測實用程序 |
.reqg 如果您不刪除其核心文件,可能會多次自行恢復. 我們建議下載 Loaris Trojan Remover 來掃描惡意實用程式. 這可以節省您大量的時間和精力,以有效地清除設備中所有可能的惡意軟件.
|
Delete Reqg Virus Ransomware
某些步驟可能會要求您退出該頁面. 書籤 以便稍後輕鬆返回.
重新啟動 安全模式 (如果您不知道如何操作,請使用本教程).
點擊 控制鍵 + 轉移 + ESC鍵 同時並轉到 進程選項卡. 嘗試識別哪些進程是惡意的.
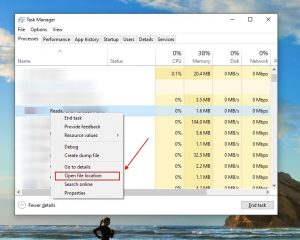
右鍵點擊 對他們每個人進行選擇 打開文件所在位置. 然後使用在線文件檢查器檢查文件:
一旦你打開他們的文件夾, 結束進程 那些被污染的, 然後 刪除他們的文件夾.
筆記:如果你特別確定某件事是威脅的一部分 - 擺脫它, 即使掃描儀沒有註意到它. 沒有任何防病毒應用程序可以識別所有感染.
繼續按住 贏 + 右. 然後復制 & 粘貼以下內容:
- 記事本%windir%/system32/Drivers/etc/hosts
將打開一個新文檔. 萬一你被黑了, 底部會有大量連結到您設備的其他 IP. 檢查下圖:
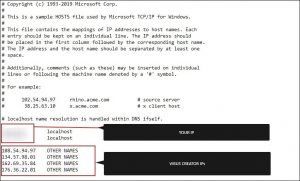
如果下面有可疑的IP“本地主機” – 在評論中與我們聯繫.
使用 控制鍵 + 轉移 + ESC鍵 同時並訪問 啟動選項卡:
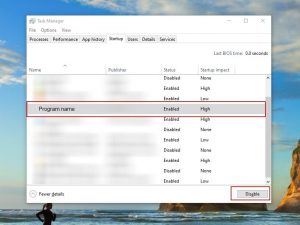
繼續 節目名稱 並選擇“禁用”.
請記住,勒索軟件甚至可能在其進程中包含虛假的開發人員名稱. 您必須檢查每個流程並確信其是合法的.
為了擺脫 Reqg Virus, 您可能需要處理系統文件和註冊表. 犯錯誤並擺脫錯誤的東西可能會損壞您的設備.
您可以選擇 Loaris Trojan Remover 來防止系統損壞 - A high-quality Reqg removal software.
閱讀有關的評論 Loaris 木馬清除器 (許可協議, 隱私政策 ).
看 為了 勒索軟件 在您的註冊表中和 擺脫 條目. 要非常小心 - 如果刪除與勒索軟件無關的條目,您可能會破壞您的系統.
在 Windows 搜索字段中鍵入以下各項:
- %應用程序數據%
- %本地應用程序數據%
- %程序數據%
- %目錄%
- %溫度%
擺脫 Temp 中的所有內容. 最後, 只需檢查最近添加的任何內容. 如果您遇到任何問題,請不要忘記給我們留言!
How to Decrypt .reqg files?
Djvu 勒索軟件本質上有兩個版本.
- 舊版: 大多數較舊的擴展 (從“.djvu”到“.carote”) 大多數這些版本的解密以前由 STOPDecrypter 工具支持 如果使用離線密鑰感染文件. 同樣的支持已納入新的 Emsisoft解密器 對於這些舊的 Djvu 變體. 如果您有文件對,解密器只會解碼您的文件而不提交文件對 離線密鑰.
- 新版本: 八月底左右發布的最新擴展 2019 勒索軟件被更改後. 這包括 .coharos, .沙裡茲, .然後, .赫塞, .農場, .瀨戶, 佩塔, .摩卡, .藥物, .嘎嘎, .愚蠢的, .卡爾, .距離, .啟動等等....這些新版本僅受 Emsisoft Decryptor 支持.
"解密器無法解密我的文件?"
在許多情況下,這意味著您有一個在線 ID. It might likewise mean your data were secured by a newer variation of STOP/Djvu.
- 離線ID. When the ransomware can't connect to its command as well as control web servers while encrypting your files, it utilizes an integrated security key and an integrated ID. 離線 ID 通常結束於 t1 and also are normally simple to identify. 鑑於離線密鑰和 ID 只是隨著每個變體/擴展而變換, everyone who has actually had their documents secured by the very same variant will have the same ID and also the files will be decryptable by the exact same key (或者 "RSA加密時的獨佔金鑰).
- 在線身份證. Most of the times the ransomware is able to link to its command and control web servers when it secures data, and also when this takes place the web servers react by creating arbitrary keys for every contaminated computer. 由於每個電腦系統都有自己的密鑰, you can not use a key from one more computer to decrypt your files. The decrypter can functioning around this with older versions as long as it has some help, 然而,對於較新的版本,無法還原文件.
如果教程沒有幫助, 下載我們建議或嘗試的反惡意軟件工具 免費在線病毒檢查器. 此外, 您可以隨時在評論中向我們尋求幫助!





發表評論