Researchers from the ThreatFabric company spoke about a new vishing scheme (aka «voice fishing»), in which attackers trick victims into installing Copybara Android malware on their devices.
Let me remind you that we also wrote that Experts described how Android malware infiltrates the Google Play Store, and also that Malware Roaming Mantis Devours Thousands of Devices around the World.
Experts have discovered a network of phishing sites targeting users of Italian banks. In fact, these resources are designed to swindle the contact details of the victims. The collected information is then used in vishing or phone-based attacks, that is, attackers call victims using data from fraudulent sites.
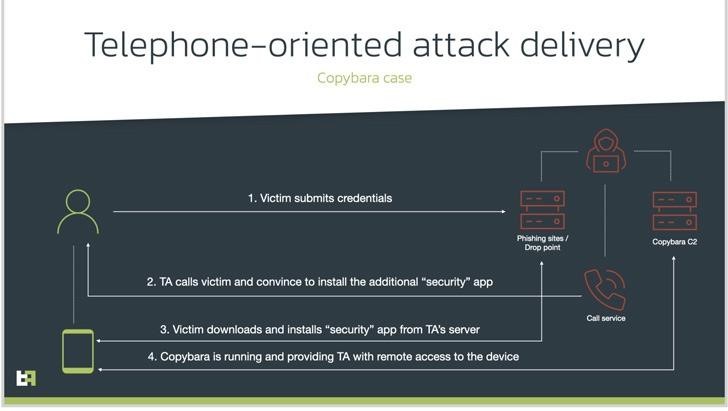
Attack Scheme
Typically, the caller poses as a bank help desk employee and instructs the person on the other end of the line to install a “security app” and grant them all the necessary permissions. In fact, this application is a malware designed to gain remote access to the device or commit financial fraud.
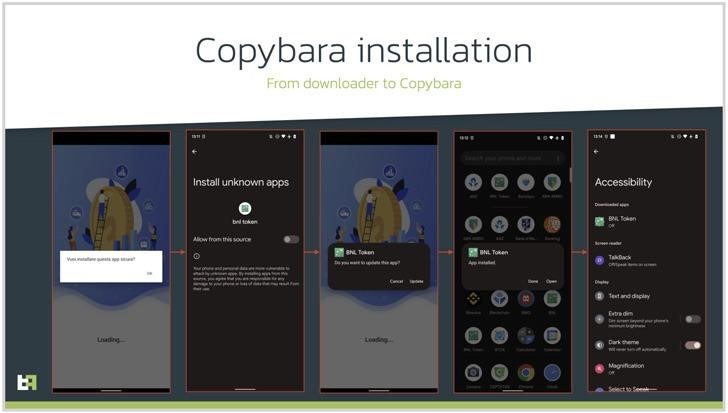
In the campaign described by the researchers, scammers distribute malware dubbed Copybara. This is a mobile Trojan first discovered back in November 2021, which is used mainly for overlay attacks targeting Italian users. Experts note that Copybara is often confused with another similar malware family known as BRATA.
According to ThreatFabric, the Copybara distribution campaign has been going on for about a year now.
Like many Android malware, RAT Copybara relies on abusing the Accessibility services API to collect sensitive information and even remove the downloader app to cover its tracks.
In addition, analysts noticed that the malware delivers another malware to the victim’s device, SMS Spy, which allows attackers to access all incoming SMS messages and intercept one-time passwords sent by banks.
Experts write that in general, such attacks are more difficult for attackers to execute and maintain, but they are becoming more popular, along with classic Google Play Store droppers, fraudulent advertising and SMS phishing.

Leave a Comment