Sophos discovered tens of thousands of variants of the WannaCry ransomware, which caused a massive epidemic in 2017. WannaCry survived and increased activity: two years later, the ransomware attacks continue and the number of vulnerable computers remains stably high.
The infamous WannaCry cryptographer that caused the global epidemic in May 2017, has not gone anywhere and is still attacking a huge number of machines around the world.
Moreover, according to Sophos experts, it is active more than ever.
In fact, it is about the number of successful infections, but about millions of attempts. The problem is that WannaCry has a huge number of variations, and there are more and more of them. To date, there are already 12.5 thousand variants of the original code. About 98% of recent detections occur in 2.7 thousand samples, which lack the very deactivation function, which made it possible to stop the epidemic in the spring of 2017.
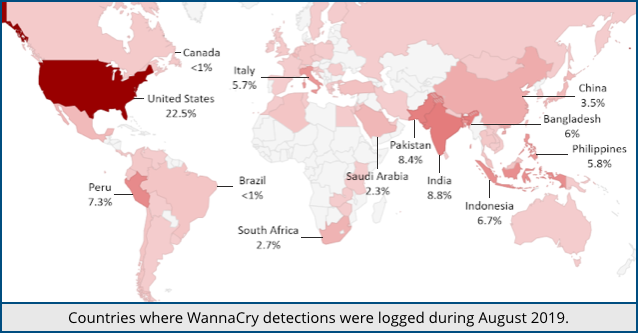
Meanwhile, only in August 2019, Sophos defensive telemetry revealed 4.3 million WannaCry samples in 6963 variants. 5555 of them, that consists 80%, were not previously detected. In other words, the active development of new variants of the ransomware continues.
“A few people actually paid the ransom even though there’s no point in doing so. The crooks behind the relevant Bitcoin addresses aren’t monitoring payments or providing decryption tools”, — reports Sophos experts Peter Mackenzie.
Sophos experts, however, found that WannaCry has a feature that allows it to defend against it: some variants of the virus check the attacked system to see if it has been infected by WannaCry before and ignore it if they find signs of infection.
Thus, the computer can literally be “vaccinated” with the help of a neutralized version of WannaCry: active malware will ignore it. However, it is not known how much such protection will last.
“If patches are not installed on time, it is not always a private problem of the owner of vulnerable systems. When it comes to vulnerabilities that can be exploited by worms such as WannaCry, each device that is not updated in time becomes a source of threat to others, ” – warn Sophos experts.
The key problem remains the abundance of computers in which the vulnerability used by WannaCry has not been fixed. It is worth recalling that the 2017 epidemic became possible because the ransomware used two exploits that leaked shortly before the events. These exploits were developed, according to the most common version, by the US National Security Agency: Eternal Blue and DoublePulsar. EternalBlue – to gain access to the system, DoublePulsar – to install and run a copy.
Read also: Researchers discovered 125 vulnerabilities in 13 models of routers and NAS
The EternalBlue exploit uses a weak spot in the implementation of the SMB protocol in versions of Windows OS (Windows 7, Windows Server 2008 and earlier) – vulnerability CVE-2017-0145, fixed by Microsoft two months before the WannaCry epidemic.

Leave a Comment