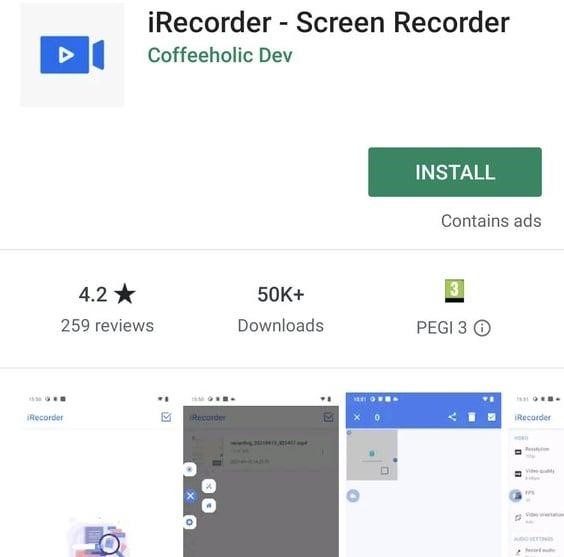
iRecorder, Screen Recorder screen recording app with over 50,000 downloads on Google Play, received a remote access trojan as an “update” and turned into a spyware.
È interessante notare, the malicious functionality appeared only a year after the application was published in the Google Play store.
Lascia che ti ricordi che abbiamo scritto anche quello Chinese Hacker Group Evasive Panda Hacked Tencent App to Spy on NGOs, e anche quello Due gruppi di hacker hanno violato contemporaneamente un'agenzia federale negli Stati Uniti utilizzando un bug vecchio di quattro anni.
ESET experts who discovered a threat in the application say that iRecorder – Screen Recorder appeared in the store in September 2021, Ma it was trojanized after an update to version 1.3.8 in August 2022.
Since the application was intended for screen recording, it made it easier for attackers to request permissions to record audio and access files on infected devices without arousing suspicion.
The malware that was included in the mentioned update is RAT AhRat, based on the open source AhMyth source code. Allo stesso tempo, the code taken from AhMyth was heavily modified, and the developer clearly knew what he was doing.
The AhRat malware has a wide range of capabilities, including tracking the location of infected devices, stealing call logs, contacts, and text messages, sending SMS messages, recording background sounds, and taking photos.
ESET experts note that the malicious screen recording application used only part of AhRat’s capabilities: every 15 minutes it recorded and transmitted background sounds to a remote server (the recording lasted about a minute), and also stole files with certain extensions, which led researchers to think about cyber espionage .

Lukáš Štefanko
The app has now been removed from Google Play, however experts warn that iRecorder – Screen Recorder may be available on alternative and unofficial Android app stores.
It should be noted that this is not the first time that malware based on open source AhMyth has penetrated Google Play. COSÌ, In 2019, the same ESET experts found Radio Balouch E RB Music apps in the store, which did contain legitimate components for streaming radio broadcasting, but were also infected with AhMyth.

Lascia un commento