IOActive researchers have demonstrated that EM fault injection (EMFI) side-channel attacks, which allow to run malicious code on the device, can be used to hack drones.
For their experiments, the researchers chose one of the popular drone models – DJI Mavic Pro. They note that DJI is a well-established manufacturer that pays special attention to the security of its products, including the use of encrypted firmware, as well as Trusted Execution Environment (TEE) and Secure Boot.
Let me remind you that we also wrote about DJI Drones Reveal Their Pilot’s Location, and also that Wolverine Experimental Project Uses AI to “Regenerate” Code on the Fly.
The media also wrote that the Financial Company Found That It Was BeingHhacked Using a Drone with WiFi Pineapple on Board.
A drone can be attacked using different vectors, including the server side, its mobile application, radio frequency communications, and the physical device itself. Experts took the path of attacking the device itself and used electromagnetic radiation to implement EMFI-type attacks.
During the first experiment, the researchers tried to use electromagnetic radiation to obtain an encryption key and use it to decrypt the firmware. They found an area on the drone’s circuit board with a strong electromagnetic signal, placed a probe there, and eventually recorded enough data to extract the key.
After identifying the zone with the strongest signal, the experts tried to figure out how to bypass the signature verification that occurs before decrypting the firmware. After several days of tests and data analysis, it was found that the probability of successfully bypassing the signature is less than 0.5%. In fact, this made key recovery impossible.
Then IOActive analysts went the other way and took as a basis the ideas previously published by Riscure specialists. In their study, they proposed to provoke a failure in order to force one instruction to transform into another and seize control, for example, of the PC registry.
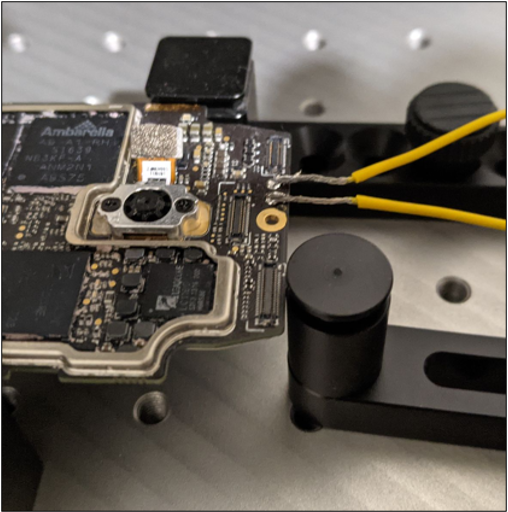
As a result, an installation was assembled in IOActive, which can be seen in the illustration below. To implement the attack, they needed a laptop (used as a controller), a power supply, a Riscure Spider (used to generate a trigger), an oscilloscope, an XYZ table, and an EMFI pulse generator.

In fact, the use of electromagnetic signals for memory corruption has been found to be applicable to the delivery of a payload that enables code execution. An attacker can use this exploit to take control of a specific device, leak sensitive data, enable ADB access, and leak encryption keys.
The researchers summarize that during these tests, they tried to understand whether such attacks on a complex and modern device are generally possible.
Since it has been proven that it is possible to take control of a device during firmware processing, the next step is to apply the experience gained on another DJI model that does not have previously known vulnerabilities and create an actual exploit.

Leave a Comment